Watching the Swiss: A network approach to rural and exurban public transport
Tim Petersen in Transport Policy:
Public transport in rural and exurban areas faces major challenges, with low population densities making it difficult to provide high-quality, high-occupancy services. While demand-responsive transport is sometimes prescribed as an innovative strategy for service provision, the network planning approach to public transport suggests that integrated timed-transfer or pulse timetable networks should be explored first. This paper examines the rural network approach using examples from Switzerland, which has among the highest rates of public transport use in Western Europe, as well as nationally-coordinated Taktfahrplan scheduling that extends deep into rural areas. The basic Swiss pulse timetabling technique is reviewed, along with the application of the approach to a remote rural case study in Graubünden’s Lower Engadine and Val Müstair.
Dirty dealing in the $175 billion Amazon Marketplace
Josh Dzieza at The Verge:
For sellers, Amazon is a quasi-state. They rely on its infrastructure — its warehouses, shipping network, financial systems, and portal to millions of customers — and pay taxes in the form of fees. They also live in terror of its rules, which often change and are harshly enforced. A cryptic email like the one Plansky received can send a seller’s business into bankruptcy, with few avenues for appeal.
Sellers are more worried about a case being opened on Amazon than in actual court, says Dave Bryant, an Amazon seller and blogger. Amazon’s judgment is swifter and less predictable, and now that the company controls nearly half of the online retail market in the US, its rulings can instantly determine the success or failure of your business, he says. “Amazon is the judge, the jury, and the executioner.”
Via Schneier on Security.
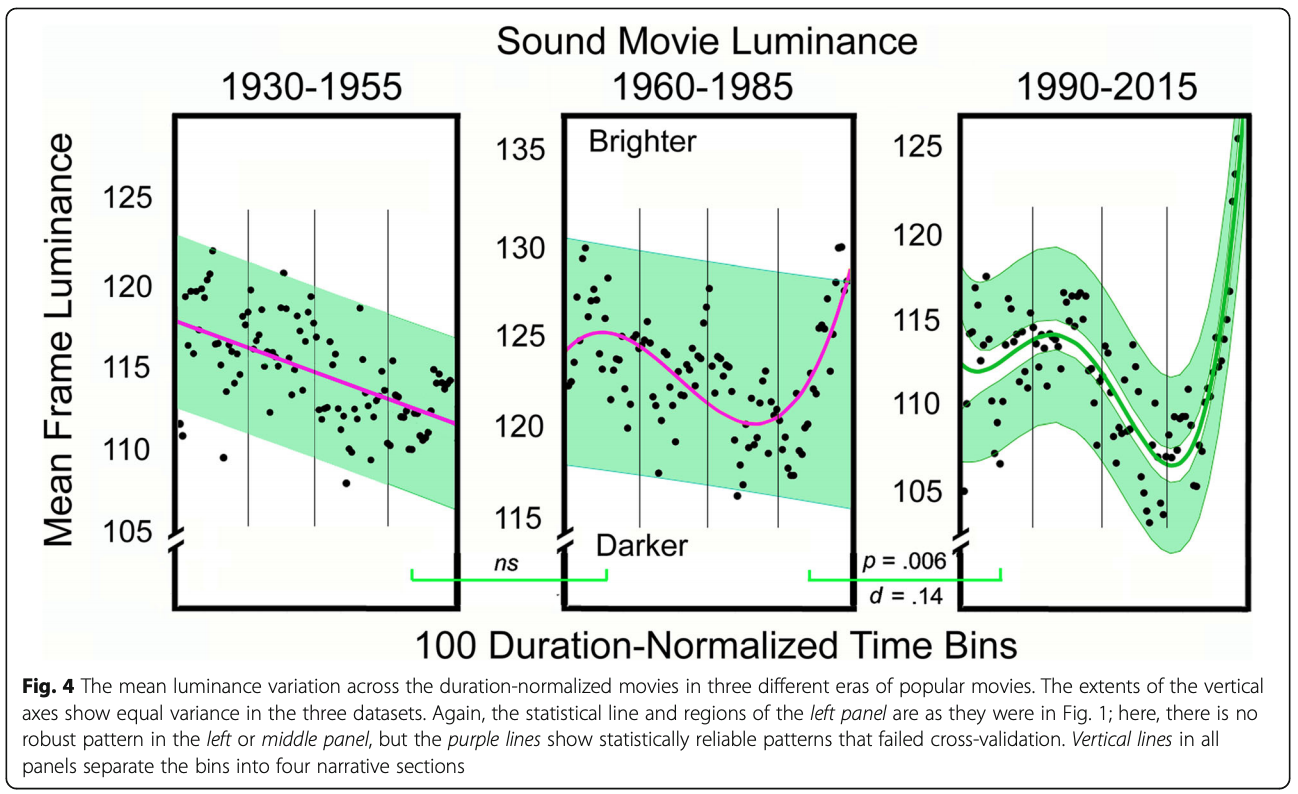
The evolution of pace in popular movies
James E. Cutting (name checks out):
Movies have changed dramatically over the last 100 years. Several of these changes in popular English-language filmmaking practice are reflected in patterns of film style as distributed over the length of movies. In particular, arrangements of shot durations, motion, and luminance have altered and come to reflect aspects of the narrative form.
The man who created the last index
This note is a work of fiction that addresses the role of indexation and passive management in investing today. It covers the origins of indexation and how the role that an index is expected to perform has now changed. The rapid growth in the number of indices presents a problem for investors in that it becomes harder to articulate what is meant by a passive investment. This leads to a discussion of the work of Borges and Balzac and what it means for investing.
Via Matt Levine.
Efficient Promotion Strategies in Hierarchical Organizations
Alessandro Pluchino, Andrea Rapisarda, Cesare Garofalo:
The Peter principle has been recently investigated by means of an agent-based simulation and its validity has been numerically corroborated. It has been confirmed that, within certain conditions, it can really influence in a negative way the efficiency of a pyramidal organization adopting meritocratic promotions. It was also found that, in order to bypass these effects, alternative promotion strategies should be adopted, as for example a random selection choice. In this paper, within the same line of research, we study promotion strategies in a more realistic hierarchical and modular organization and we show the robustness of our previous results, extending their validity to a more general context. We discuss also why the adoption of these strategies could be useful for real organizations.
How important is economic growth?
Scott Sumner with a bit of wisdom in a review of Tyler Cowen’s Stubborn Attachments:
Unfortunately, when discussing redistribution, our society tends to focus on income, which is the wrong variable. Yes, the rich might invest an extra dollar in income, thereby helping future generations. But that’s not relevant to the real issue, which is consumption redistribution. One commenter suggested that it might be better if I invested $10,000 rather than donate the money to a family in Ethiopia. But that’s dodging the real question—don’t I have an ethical obligation to donate $10,000 of my current consumption? The rich should never feel any guilt about investing money rather than giving it to charity. Where they perhaps should feel a bit of guilt is in spending $500 million on consumption, rather than donating a significant share of those funds to the poor.
Human Images From World’s 1st Total-Body Scanner Unveiled
Explorer, the world’s first medical imaging scanner that can capture a 3D picture of the whole human body at once, has produced its first scans.
Movie tracing the delivery and distribution of a radiolabeled sugar (fluorodeoxyglucose) following injection into a leg vein. In the first few seconds following injection it travels to the heart from where it is distributed through the arteries to all the organs of the body. At around 3 minutes, some of the substance is excreted from the kidneys into the bladder. Gradual accumulation of the glucose can be seen in the heart, brain and liver over time. The EXPLORER scanner will allow the delivery, metabolism and excretion of many substances and drugs to be followed in the entire human body in a similar manner.
St Fagans
Christopher Schwarz at Lost Art Press:
For at least the 12th time this month I’ve looked at the work on my bench and found that the odder it looks, the better.
I’m building a near-replica of a chair on display at St Fagans National Museum of History, and replica work is not usually my bag (or it hasn’t been for a long, long time). At every turn, this chair does the opposite of what I would do if it were my design. But I vowed to stick as close to the original as possible.
Why am I doing this? To attempt get inside the head of the original Welsh maker and perhaps learn something.
Classicool
In Classicool the subjects of the paintings abandon their classical pose by literally taking the canvas to “paint themselves”.
Via BruceS.
Tech C.E.O.s Are in Love With Their Principal Doomsayer
Nellie Bowles in The New York Times with a profile of Yuval Noah Harari (use the archive link to bypass the paywall):
His prophecies might have made him a Cassandra in Silicon Valley, or at the very least an unwelcome presence. Instead, he has had to reconcile himself to the locals’ strange delight. “If you make people start thinking far more deeply and seriously about these issues,” he told me, sounding weary, “some of the things they will think about might not be what you want them to think about.”
What if the Placebo Effect Isn’t a Trick?
Gary Greenberg at The New York Times (Use archive link to bypass paywall):
Two dozen of the leading lights of placebo science spent a preconference day agonizing over their reputation — as purveyors of sham medicine who prey on the desperate and, if they are lucky, fool people into feeling better — and strategizing about how to improve it. It’s an urgent subject for them, and only in part because, like all apostate professionals, they crave mainstream acceptance. More important, they are motivated by a conviction that the placebo is a powerful medical treatment that is ignored by doctors only at their patients’ expense.
And after a quarter-century of hard work, they have abundant evidence to prove it. Give people a sugar pill, they have shown, and those patients — especially if they have one of the chronic, stress-related conditions that register the strongest placebo effects and if the treatment is delivered by someone in whom they have confidence — will improve.
John Urschel Goes Pro
Jordan Ellenberg at Hmm Daily:
“I have, or had, more math talent than football talent,” Urschel tells me. “I fully believe this.” But the world is on the lookout for football players. His coaches at Canisius, an all-boys Jesuit high school, continually encouraged him to think big, bigger, biggest. If he worked at it, he could play in college. He could play in the Big Ten. There was a chance he could play in the NFL. From his math teachers? Zero.
That changed at Penn State, where Urschel enrolled in 2009 to study math and play football.
Kinematics of the Interstellar Vagabond 1I/'Oumuamua
When the velocity is compared to the local stars, ‘Oumuamua can be ruled out as co-moving with any of the dozen nearest systems, i.e. it does not appear to be associated with any local exo-Oort clouds (most notably that of the Alpha Centauri triple system). ‘Oumuamua’s velocity is within 5 km/s of the median Galactic velocity of the stars in the solar neighborhood (<25 pc), and within 2 km/s of the mean velocity of the local M dwarfs. Its velocity appears to be statistically “too” typical for a body whose velocity was drawn from the Galactic velocity distribution of the local stars (i.e. less than 1 in 500 field stars in the solar neighborhood would have a velocity so close to the median UVW velocity). In the Local Standard of Rest frame (circular Galactic motion), ‘Oumuamua is remarkable for showing both negligible radial (U) and vertical (W) motion, while having a slightly sub-Keplerian circular velocity (V; by ~11 km/s). These calculations strengthen the interpretation that A/2017 U1 has a distant extrasolar origin, but not among the very nearest stars. Any formation mechanism for this interstellar asteroid should account for the coincidence of ‘Oumuamua’s velocity being so close to the LSR.
Via Centauri Dreams via MR
Japan's Hometown Tax
The Japanese employment market has a curious feature: there are regions of Japan with extremely high economic productivity (such as Tokyo, Osaka, and Nagoya, but for the purpose of this issue think “Tokyo” and you won’t be wrong) and regions with low economic productivity (substantially everywhere else). This counsels that a young person born and educated in e.g. Gifu move to Tokyo after graduation to earn a living.
Many, many do. While Japan’s overall population is declining, Tokyo’s increases by about 100,000 people per year.
Educating children is incredibly expensive. The regions are quite annoyed that they pay to educate their children but that Tokyo reaps all the benefits. This state of affairs has continued for decades.
But Japan has a policy response for it, and it is sort of beautiful. Called ふるさと納税 (Furusato Nouzei or, roughly, the Hometown Tax System) [ … ]
Via Matt Levine.