Things tagged tech:
Gender Swap - Experiment with The Machine to Be Another on Vimeo
Gender Swap is an experiment that uses themachinetobeanother.org/ system as a platform for embodiment experience (a neuroscience technique in which users can feel themselves like if they were in a different body). In order to create the brain ilusion we use the immersive Head Mounted Display Oculus Rift, and first-person cameras. To create this perception, both users have to synchronize their movements. If one does not correspond to the movement of the other, the embodiment experience does not work. It means that both users have to constantly agree on every movement they make. Through out this experiment, we aim to investigate issues like Gender Identity, Queer Theory, feminist technoscience, Intimacy and Mutual Respect.
Einstein’s Camera
Fantastic profile of one of my favorite artists:
Joshua Hammer in Matter:
Adam Magyar is a computer geek, a college dropout, a self-taught photographer, a high-tech Rube Goldberg, a world traveler, and a conceptual artist of growing global acclaim. But nobody had ever suggested that he might also be a terrorist until the morning that he descended into the Union Square subway station in New York.
Case Study: Ender's Game on Vimeo
Light Iron takes you step by step through the progressive data management and color pipeline of Ender’s Game.
Not a fan of the creative, but the tech is cool.
Algorithms and Speech
Stuart Minor Benjamin in the University of Pennsylvania Law Review:
More and more of our activity involves not merely the transmission of bits, but the transmission of bits according to algorithms and protocols created by humans and implemented by machines. Messages travel over the Internet because of transmission protocols, coding decisions determine the look and feel of websites, and algorithms determine which links, messages, or stories rise to the top of search engine results and web aggregators’ webpages. Most webpages have automated components, as do most online articles and all video games. Are these algorithm-based outputs “speech” for purposes of the First Amendment? That is, does the Free Speech Clause of the First Amendment apply to government regulation of these or other algorithm based changes to bits?
More then you ever wanted to know about jet turbines
Spent about 6 hours of my day off nerding out over this guys videos. All you ever wanted to know about power turbines.
New Mobile Obsession: U.S. Teens Triple Data Usage - Nielsen
Messaging remains the centerpiece of mobile teen behavior. The number of messages exchanged monthly (SMS and MMS) hit 3,417 per teen in Q3 2011, averaging seven messages per waking hour. Teen females are holding the messaging front, sending and receiving 3,952 messages per month versus 2,815 from males.
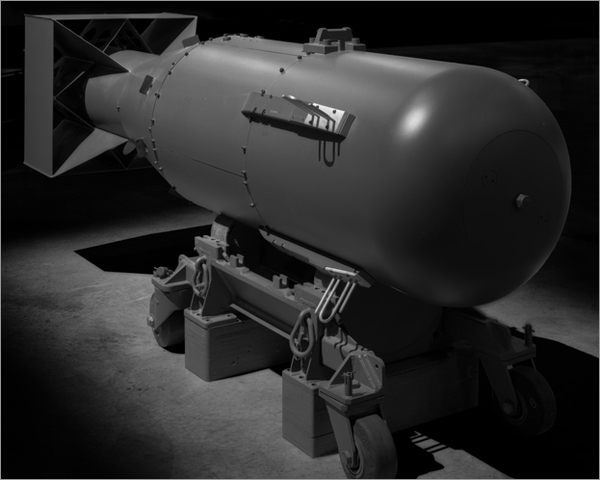
Weapons of Mass Destruction
“Little Boy” (Hiroshima Atomic Bomb) 1945
Nice set of black and white (and infrared?) photos of cold war era Weapons of Mass Destruction.
See also: “Atomic John” in The New Yorker
The single, blinding release of pure energy over Hiroshima, Japan, on August 6, 1945, marked a startling and permanent break with our prior understandings of the visible world. Yet for more than sixty years the technology behind the explosion has remained a state secret.
The most accurate account of the bomb’s inner workings—an unnervingly detailed reconstruction, based on old photographs and documents—has been written by a sixty-one-year-old truck driver from Waukesha, Wisconsin, named John Coster-Mullen, who was once a commercial photographer, and has never received a college degree.
An Engineering Evaluation of SHA-3 candidates
Niels [Ferguson, of the Skein team] has started a page of SHA-3 engineering comparisons.
Yes, they are biased, but I still trust the results.
Via Schneier on Security.
Beijing Cubism: How ETFE Revolutionized the Bubble
ETFE is temperature-resistant, lightweight (1/100th the weight of glass), recyclable, non-toxic when exposed to flame (it actually shrinks away from heat, thus helping to vent smoke out of a burning building), highly insulative, non-porous, and non-stick. Even better, its high-tensile strength makes it easy to manipulate—it can be spun into thin sheets for ease of transport then inflated on-site to create the “pillow” effect of the Aquatics Center walls. It can also be finished in varying degrees of translucence—as transparent as glass or opaque as glass bricks.
Via at cityofsound.
What Sun Should Do
Tim Bray on Sun:
Sun is going through a lousy spell right now. Well, so is the world’s economy in general and the IT business in particular, but this is about Sun. This is my opinion about what my employer should do about it. [. . .] Sun should adopt a laser focus on building a Sun Web Suite and becoming the Web application deployment platform of choice. It’s a large space, a growing space, and one where we can win.
He is obviously absolutely right, there is no place for the old Sun in this world. However Sun does have some excellent tech, and importantly they seem to still have a lot of top engineers, so if they can manage a major restructuring they have a fighting chance.
Shirky on Coase, Collaboration and Here Comes Everybody
Clay Shirky, author of Here Comes Everybody: The Power of Organizing Without Organizations, talks about the economics of organizations with EconTalk host Russ Roberts. The conversation centers on Shirky’s book. Topics include Coase on the theory of the firm, the power of sharing information on the internet, the economics of altruism, and the creation of Wikipedia.
And a great bit of discussion on representative vs. direct democracy and the possibility that networks can enable direct democracy.
Via EconLog.
The Mother of All Maker Zen Clips
Bruce Sterling at Beyond the Beyond:
*This French guy is serenely hand-manufacturing his own vacuum tubes.
*This video is seventeen minutes long. I’d also be guessing this gentleman has invested about seventeen years in acquiring that vacuum-tube zen.
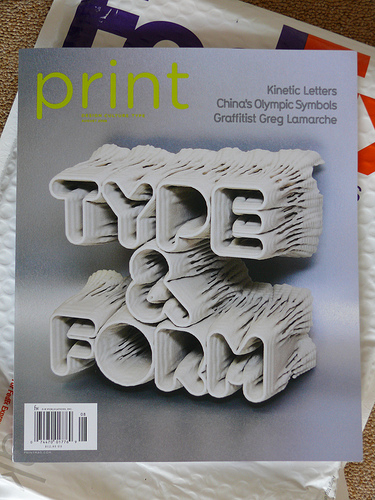
Generation. Man, now that's typography.
Late in April the super friendly people from Print Magazine commissioned me to create a cover design which would conceptually support the main feature article about “kinetic typography” of their special summer issue.
Via Bruce Sterling at Beyond the Beyond.
How to be an instant Web me-2.0 developer
The first, most basic, skill: be able to distinguish the different versions of the web.
Web versions, 1.0 to 2.0 Version Characteristics Web 1.0 Programming model equivalent to that of a slightly up-market 3270 terminal. Forms are filled in with the sequence: tab tab tab tab tab tab bonk.Web 1.00001 The beginning of the rich web experience: the first ever, primitive Javascript code fragment is written. It generates an unwanted popup, and snaffles your credit card details. Web 1.1 No visible difference from Web 1.0, apart from IE showing the text 'Javascript error' in its status bar. Web 1.2 Standard buttons are upgraded with smart 3D-looking GIFs. These react to mouseover events by bobbing up and down politely over their drop shadows. Remember when we were excited by this sort of scriptery? (None of your CSS cleverness then.) It seems so quaint now. It makes me want to cry, thinking about the good old days of ugly web pages loading slowly. Web 1.3 When you get to the home page of a V1.2 site with FireFox, it displays badly. When you go to a V1.3 website such as www.fdms.com with FireFox, it tells you to eff off and get IE. (These traditionalists in fact would seem to prefer it if you used IE4.) The age of 'you aren't good enough for our website' has begun, reaching full fruition at Web 1.5, see below. Web 1.4 Basic client-side validation added. Forms are filled in with the sequence: tab tab tab tab tab What do you mean 'invalid post code' you bloody thing?The dread phrase 'next generation of 3d smileys' is encountered for the very first time.
Via Tim Bray.
Beautiful Machinery
Sculptor and engineer Arthur Ganson talks about his work -- kinetic art that explores deep philosophical ideas and is gee-whiz fun to look at.
Via Wohba!.
Dynamic Languages Strike Back
Some guys at Stanford invited me to speak at their EE Computer Systems Colloquium last week. Pretty cool, eh? It was quite an honor. I wound up giving a talk on dynamic languages: the tools, the performance, the history, the religion, everything. It was a lot of fun, and it went over surprisingly well, all things considered.
Via Tim Bray.
Microsoft acquires Stefan Brands (patents and friends)
Posted by iang to Financial Cryptography.
Interesting news: According to the posts over at identity corner, Microsoft is picking up (some of? all of?) Credentica's patent portfolio, and Stefan Brands himself will join the team.
Brands has one (of two) lineages of patents on digital blinding, the other one was via David Chaum, and is now lost somewhere in some bank's hands due to bankruptcy. Though Chaum was working on something new, haven't heard anything about that . . . Anyhow, this means Microsoft is in control of the current state of the art for digital money, and identity management.
Congratulations - it must have been a fantastic monetary offer to make you withdraw credentials from the open market like this and hand over control of identity to MS.This just set [Privacy Enhancing Technologies] back many years.
And Kim Cameron (Microsoft) has a great round up of the PR and reactions in the wake of the announcement at identityblog: Reactions to Credentica acquisition
He ends with:
That doesn’t mean it is trivial to figure out the best legal mecahnisms for making the intellectual property and even the code available to the ecosystem. Lawyers are needed, and it takes a while. But I can guarantee everyone that I have zero intention of hoarding Minimal Disclosure Tokens or turning U-Prove into a proprietary Microsoft technology silo.
Sure you don't, but what about your evil overlords?