Things tagged freespeech:
François Chollet on Twitter
François Chollet, an AI expert at google on Twitter:
The problem with Facebook is not just the loss of your privacy and the fact that it can be used as a totalitarian panopticon. The more worrying issue, in my opinion, is its use of digital information consumption as a psychological control vector. Time for a thread
My Life as a New York Times Reporter in the Shadow of the War on Terror
James Risen in The Intercept:
My case was part of a broader crackdown on reporters and whistleblowers that had begun during the presidency of George W. Bush and continued far more aggressively under the Obama administration, which had already prosecuted more leak cases than all previous administrations combined. Obama officials seemed determined to use criminal leak investigations to limit reporting on national security. But the crackdown on leaks only applied to low-level dissenters; top officials caught up in leak investigations, like former CIA Director David Petraeus, were still treated with kid gloves.
[…]
But even as I was losing in the courts, I was gaining ground in the court of public opinion. My decision to go to the Supreme Court had captured the attention of the nation’s political and media classes. Instead of ignoring the case, as they had for years, the national media now framed it as a major constitutional battle over press freedom.
[…]
I was worried, but I felt certain that the hearing would somehow complete the long, strange arc I had been living as a national security investigative reporter for the past 20 years. As I took the stand, I thought about how I had ended up here, how much press freedom had been lost, and how drastically the job of national security reporting had changed in the post-9/11 era.
Snowden's Boss Shares Lessons Learned
A few words from the other side. Worth considering, as we don’t get a chance often.
The man who was Edward Snowden’s boss when the National Security Agency (NSA) leaker fled the United States is now speaking out about his experiences and how to counter insider threats.
Steven Bay, who served as Snowden’s boss when he worked as a NSA contractor with Booz Allen Hamilton from April 1 to May 20, 2013, told The Cipher Brief he has decided to publicly discuss his brief time working with the NSA leaker to fill out a “gap in the history” and combat what he calls a wealth of “misinformation that’s out there.”
Secret Cameras Record Baltimore’s Every Move From Above
Monte Reel in Bloomberg Businessweek:
Pritchett had no idea that as he spoke, a small Cessna airplane equipped with a sophisticated array of cameras was circling Baltimore at roughly the same altitude as the massing clouds. The plane’s wide-angle cameras captured an area of roughly 30 square miles and continuously transmitted real-time images to analysts on the ground. The footage from the plane was instantly archived and stored on massive hard drives, allowing analysts to review it weeks later if necessary.
Since the beginning of the year, the Baltimore Police Department had been using the plane to investigate all sorts of crimes, from property thefts to shootings. The Cessna sometimes flew above the city for as many as 10 hours a day, and the public had no idea it was there.
The city wide panopticon that can solve crimes by rewinding time.
Financial Cryptography 2016
Ross Anderson at Light Blue Touchpaper has livebloged Financial Cryptography 2016. Lots of good stuff!
Preliminary thoughts on the Apple iPhone order in the San Bernardino case: Part 3, the policy question
Orin Kerr in The Volokh Conspiracy:
In this post, the third in a series, I want to discuss what I think is the policy question at the heart of the Apple case about opening the San Bernardino iPhone. The question is, what is the optimal amount of physical box security? It’s a question we’ve never asked before because we haven’t lived in a world where a lot of physical box security was possible. Computers and cellphones change that, raising for the first time the question of how much security is ideal.
A Message to Our Customers
Tim Cook at apple.com:
The United States government has demanded that Apple take an unprecedented step which threatens the security of our customers. We oppose this order, which has implications far beyond the legal case at hand.
This moment calls for public discussion, and we want our customers and people around the country to understand what is at stake.
About time a corporation stood up, the telecoms sure haven’t, so Apple took on the role, and now have the opportunity to make a needed stand.
Judge to DOJ: Not All Writs
And Andrew Crocker at the EFF explains why the goverment is overreaching with the use of All Writs:
Reengineering iOS and breaking any number of Apple’s promises to its customers is the definition of an unreasonable burden. As the Ninth Circuit put it in a case interpreting technical assistance in a different context, private companies’ obligations to assist the government have “not extended to circumstances in which there is a complete disruption of a service they offer to a customer as part of their business.” What’s more, such an order would be unconstitutional. Code is speech, and forcing Apple to push backdoored updates would constitute “compelled speech” in violation of the First Amendment. It would raise Fourth and Fifth Amendment issues as well. Most important, Apple’s choice to offer device encryption controlled entirely by the user is both entirely legal and in line with the expert consensus on security best practices. It would be extremely wrong-headed for Congress to require third-party access to encrypted devices, but unless it does, Apple can’t be forced to do so under the All Writs Act.
Via darringfireball
The Case of the Missing Hong Kong Book Publishers
Jiayang Fan in The New Yorker:
When a politically problematic figure disappears—or is disappeared—in China, a dark uneasiness falls, though usually accompanied by a glum sense of the inevitable. This is the cost of living within an authoritarian regime with diminishing patience for deviance. For a breather from such oppressive strictures, one might hop across the border to Hong Kong, where the policy of “one country, two systems” guarantees the freedom of speech and of the press, under the former British colony’s Basic Law, its own mini-Constitution. That refuge had seemed reasonably dependable, at least until a week ago, when Lee Bo became the fifth member of a Hong Kong-based publishing house specializing in provocative tomes about Beijing leaders to vanish mysteriously, not on a trip to the mainland but from his own home city, Hong Kong.
Did Carnegie Mellon Attack Tor for the FBI?
The behavior of the researchers is reprehensible, but the real issue is that CERT Coordination Center (CERT/CC) has lost its credibility as an honest broker. The researchers discovered this vulnerability and submitted it to CERT. Neither the researchers nor CERT disclosed this vulnerability to the Tor Project. Instead, the researchers apparently used this vulnerability to deanonymize a large number of hidden service visitors and provide the information to the FBI.
Does anyone still trust CERT to behave in the Internet’s best interests?
The Web We Have to Save
Seven months ago, I sat down at the small table in the kitchen of my 1960s apartment, nestled on the top floor of a building in a vibrant central neighbourhood of Tehran, and I did something I had done thousands of times previously. I opened my laptop and posted to my new blog. This, though, was the first time in six years. And it nearly broke my heart.
You should really read that, powerful stuff.
For me, I feel like the solution is a re-emergence of the cultural elite on the web, as it was to a large degree in the late 90’s early 00’s. Then it was the whole web that was the elite, by definition. Now it will be self selected group(s), rejecting the draw of commercialism, and mass appeal, and returning to a smaller community of people who care about discourse. The good news is that this community will no longer be elite by virtue of privilege, but by choice and self selection. Bloggers who whine that only 800 people read their blog on the web, but get 40k impressions on FB? Ok, you are making a choice. People who chose to write to the 800 readers are joining a different community.
The Social Laboratory
In October 2002, Peter Ho, the permanent secretary of defense for the tiny island city-state of Singapore, paid a visit to the offices of the Defense Advanced Research Projects Agency (DARPA), the U.S. Defense Department’s R&D outfit best known for developing the M16 rifle, stealth aircraft technology, and the Internet. Ho didn’t want to talk about military hardware. Rather, he had made the daylong plane trip to meet with retired Navy Rear Adm. John Poindexter, one of DARPA’s then-senior program directors and a former national security advisor to President Ronald Reagan. Ho had heard that Poindexter was running a novel experiment to harness enormous amounts of electronic information and analyze it for patterns of suspicious activity – mainly potential terrorist attacks.
Al Goldstein, a Publisher Who Took the Romance Out of Sex, Dies at 77
Andy Newman in the NYT:
Mr. Goldstein did not invent the dirty magazine, but he was the first to present it to a wide audience without the slightest pretense of classiness or subtlety. Sex as depicted in Screw was seldom pretty, romantic or even particularly sexy. It was, primarily, a business, with consumers and suppliers like any other.
The manifesto in Screw’s debut issue in 1968 was succinct. “We promise never to ink out a pubic hair or chalk out an organ,” it read. “We will apologize for nothing. We will uncover the entire world of sex. We will be the Consumer Reports of sex.”
How Laura Poitras Helped Snowden Spill His Secrets
Peter Maass in the NYT:
Before long, Poitras received an encrypted message that outlined a number of secret surveillance programs run by the government. She had heard of one of them but not the others. After describing each program, the stranger wrote some version of the phrase, “This I can prove.”
Seconds after she decrypted and read the e-mail, Poitras disconnected from the Internet and removed the message from her computer. “I thought, O.K., if this is true, my life just changed,” she told me last month. “It was staggering, what he claimed to know and be able to provide. I just knew that I had to change everything.”
Statement from Edward Snowden in Moscow
In the end the Obama administration is not afraid of whistleblowers like me, Bradley Manning or Thomas Drake. We are stateless, imprisoned, or powerless. No, the Obama administration is afraid of you. It is afraid of an informed, angry public demanding the constitutional government it was promised — and it should be.
YouTomb
YouTomb is a research project by MIT Free Culture that tracks videos taken down from YouTube for alleged copyright violation.More specifically, YouTomb continually monitors the most popular videos on YouTube for copyright-related takedowns. Any information available in the metadata is retained, including who issued the complaint and how long the video was up before takedown. The goal of the project is to identify how YouTube recognizes potential copyright violations as well as to aggregate mistakes made by the algorithm.
Via Justin
Microsoft acquires Stefan Brands (patents and friends)
Posted by iang to Financial Cryptography.
Interesting news: According to the posts over at identity corner, Microsoft is picking up (some of? all of?) Credentica's patent portfolio, and Stefan Brands himself will join the team.
Brands has one (of two) lineages of patents on digital blinding, the other one was via David Chaum, and is now lost somewhere in some bank's hands due to bankruptcy. Though Chaum was working on something new, haven't heard anything about that . . . Anyhow, this means Microsoft is in control of the current state of the art for digital money, and identity management.
Congratulations - it must have been a fantastic monetary offer to make you withdraw credentials from the open market like this and hand over control of identity to MS.This just set [Privacy Enhancing Technologies] back many years.
And Kim Cameron (Microsoft) has a great round up of the PR and reactions in the wake of the announcement at identityblog: Reactions to Credentica acquisition
He ends with:
That doesn’t mean it is trivial to figure out the best legal mecahnisms for making the intellectual property and even the code available to the ecosystem. Lawyers are needed, and it takes a while. But I can guarantee everyone that I have zero intention of hoarding Minimal Disclosure Tokens or turning U-Prove into a proprietary Microsoft technology silo.
Sure you don't, but what about your evil overlords?
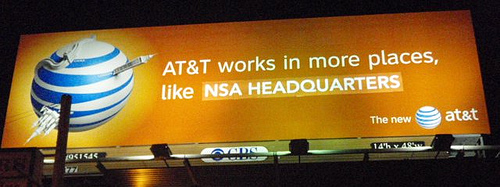
The BLF brings us AT&T "In More Places"
“This campaign is an extraordinary rendition of a public-private partnership,” observed BLF spokesperson Blank DeCoverly. “These two titans of telecom have a long and intimate relationship, dating back to the age of the telegraph. In these dark days of Terrorism, that should be a comfort to every law-abiding citizen with nothing to hide.”
Via 27B Stroke 6.